Stopping the GandCrab Scourge
- By Tim Liu, Hillstone Networks
- December 17, 2018
The GandCrab ransomware family emerged in late February 2018 and was quickly adopted by cybercriminals because it offered something no other ransomware family had offered before: custom ransom notes. While the average user would be reluctant to spend as much as USD 500 to get their data back, organizations and companies that manage client databases or have intellectual property on their servers would be far more interested in paying larger amounts of money.
Currently, the most prolific versions of GandCrab are versions 4 and 5, which are estimated to have infected around 500,000 victims worldwide, as of July 2018. Considering the lowest ransom note is USD 600 and almost half of infected victims give in to ransomware, the developers might have made at least USD 300 million in the past couple of months alone. And actual financial losses could be significantly higher, considering that some victims have reported a ransom note of USD 700,000.
At present, GandCrab combines phishing emails, webpage Trojans, vulnerability exploits, RDP brute force cracking, botnets and other attack methods to penetrate. After successful penetration, it begins to encrypt the core data stored in internal systems. Information about the ransom is shown in *-DECRYPT.TXT file.
By executing GandCrab in a virtual system, we have discovered its potential malicious behavior, the tremendous damage to business systems and core data, as well as the economic and productivity impact on enterprises and users. A comprehensive threat detection solution is needed for this security breach.
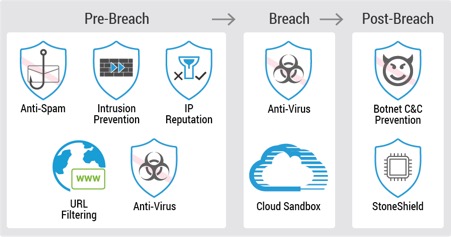
Pre-breach: blocking vulnerability exploits and brute force attacks
The execution pattern and different attack methods of the ransomware can easily be detected through a combination of anti-spam, intrusion prevention, IP reputation, URL filtering and anti-virus. It blocks vulnerability exploits and intercepts brute force attacks. The ransomware variants can then be discovered quickly to ensure protection at the network perimeter.
- Antispam: The Antispam function enables users to identify and filter mails transmitted by SMTP and POP3 protocol through the cloud server, discover the mail threat such as spam, phishing and worm mail, in a timely manner, and then process the found spam according to the configuration, so as to protect the user's mail client or mail server.
- IPS, or Intrusion Prevention System: IPS is designed to monitor various network attacks in real time and take appropriate action (log/block) against the attacks according to the configuration. The IPS can implement a complete state-based detection which significantly reduces the false positive rate. Even if the device is enabled with multiple application layer detections, enabling IPS will not cause any noticeable performance degradation.
- URL filtering: It controls access to specific websites and records log messages for all access.
- Perimeter Traffic Filtering: It filters the perimeter traffic based on known risky IPs, and takes appropriate action (log/block) on the malicious traffic that hits the list. The IP Reputation list retrieves the risky IP (such as Botnet, Spam, Tor nodes, Compromised, Brute-forcer, and so on) list from the Perimeter Traffic Filtering signature database.
Breach: Leveraging cloud sandbox
To address advanced malware, a cloud sandbox delivers a unique, advanced threat detection platform that can emulate the execution environment and analyze all activities related to malicious files, identify advanced threats and collaborate with existing solutions to provide rapid remediation. Together with virus filtering, the cloud sandbox can eradicate Gandcrab.
Post-breach: Against the infected host connecting to the Command and Control server
Botnet uses one or more means of communication to infect a large number of hosts with bots, forming a one-to-many controlled network between the controller and the infected host, which will cause a great threat to network and data security.
The botnet C&C prevention function can detect the botnet host in the internal network, as well as locate and take other actions according to the configuration, so as to avoid further threat attacks.
In addition, the botnet C&C prevention configurations are based on security zones or policies. If the botnet C&C prevention profile is bound to a security zone, the system will detect the traffic destined to the specified security zone based on the profile configuration. If the botnet C&C prevention profile is bound to a policy rule, the system will detect the traffic matched to the specified policy rule based on the profile configuration.
Conclusion
As long as there are hackers, ransomware and cyber threats, we will have to be vigilant in protecting our critical data. Ensure you have the right solution that ensures the appropriate security measures are in place at every step of the chain in protecting networks and critical assets.
Tim Liu, CTO, Hillstone Networks authored this article.
The views and opinions expressed in this article are those of the author and do not necessarily reflect those of CDOTrends.