Don’t Underestimate the Role of Network Data in Security
- By Mike Campfield, ExtraHop
- June 15, 2020
According to IDC, spending on security solutions in the Asia Pacific region is expected to reach USD 34 billion by 2023, growing at a CAGR of about 20% between 2018 and 2023. With that much money on the line, organizations have to get smarter about how their solutions work together to build the most effective security strategy, given the limited resources available.
Organizations with complex and sophisticated IT environments are increasingly migrating to the cloud. Most begin this process with a “lift and shift” of less critical applications. On the surface this seems easier than rearchitecting an application, but there are hidden complexities.
While it takes longer, the more mission critical an application the more likely that it will be rearchitected to become cloud-native to take advantage of scale in the cloud and reduce management overhead. Ultimately, most organizations, especially the larger they are, will be operating in hybrid environments.
In most large enterprises with hybrid networks, it is not uncommon to have dozens of security tools deployed in production resulting in a patchwork of isolated tools and layers of siloed defenses that can leave an organization vulnerable.
These tools, for the most part, focus on North-South traffic, meaning that once an attacker is inside the East-West traffic remains unmonitored. With increasingly sophisticated threats, an expanding attack surface, and understaffed and overworked security teams, organizations need to monitor the entire hybrid landscape to detect threats before they cause harm.
The secret is to get more value from a powerful asset they already have: network data.
Learning from the Cold War
The Security Operations Center (SOC) Visibility Triad is a concept coined by Gartner that is analogous to the “nuclear triad” concept from the Cold War. The SOC Triad combines three foundational tools: security incident and event management (SIEM), endpoint detection and response (EDR), and network traffic analysis, also known as network detection and response (NDR).
Anton Chuvakin first introduced the concept in 2015, which “seeks to significantly reduce the chance that the attacker will operate on your network long enough to accomplish their goals.”
This is not just “another model” to file away. The SOC Visibility Triad signifies a massive paradigm shift in cybersecurity, for two reasons.
First, it shifts the focus of security operations from the perimeter to the inside of the network and pivots from a "protect and prevent" mindset to a "detect and respond" mindset. For enterprises today, it is no longer enough to rely on the ingress/egress (North-South) threat prevention model, they need to take a more realistic approach that focuses on detecting threats that have circumvented the firewall, are living off the land and have extended their reach inside the enterprise environment. Adopting the SOC Visibility Triad is a step toward accepting that breaches will happen, and that knowing how to detect, respond and remediate effectively is the correct path forward.
Second, the SOC Triad endorses a critical-asset focused and data-driven security strategy — using logs, endpoints, and network traffic. The intelligence derived from these sources will enable businesses to detect threats, identify and secure their critical assets, and remediate attacks in real time.
Organize your toolbox
Log data gathered in SIEM is a mainstay of security operations because it provides a convenient record of what actions were performed, down to the device level.
One drawback is that logs are vulnerable to tampering: attackers can cover their tracks by turning off, modifying or erasing log files. Logs can also require a lot of labor, expertise, and technology investment to store, analyze, and extract their value, and therefore are often too expensive to deploy across the entire organization.
EDR platforms leveraging endpoint data are essential to a layered defense because they provide insight into user and software activities on devices, detect threats that antivirus software misses, and help monitor against advanced persistent threats. EDR’s weakness is its reliance on software agents that can be disabled or tampered with by savvy attackers and do not provide context about broader attack campaigns in progress.
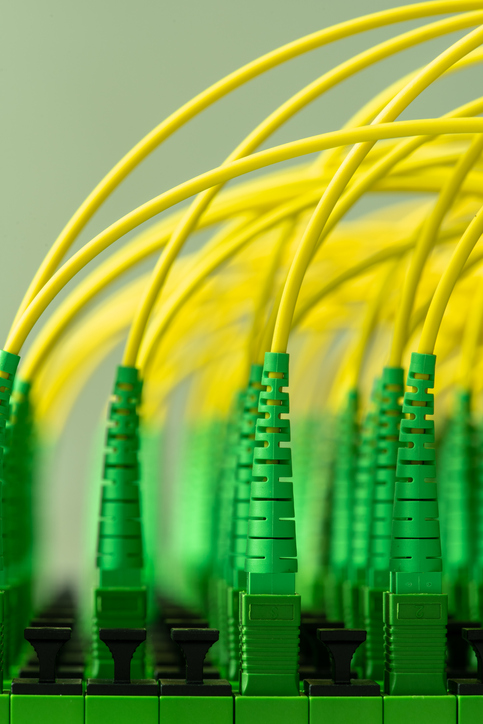
Wire data from the network includes layers 2 to 7 communications between each system and device across the entire environment (East-West traffic). It is considered the most objective ground source of truth for security investigations. If it happened on the wire, it happened.
The challenge with network data is its massive volume that is only continuing to grow. Further, the cloud has both accelerated and complicated the network environments of growing enterprises. This is creating friction in the data acquisition process when more endpoints and activity logs are added to the network. NDR solutions collect and analyze network data whether on-premises or in the cloud, complementing both EDR and SIEM and completing the SOC Triad.
The triumvirate advantage
The core benefit of adopting the SOC Triad is complete visibility into network communications, endpoints, and events. This comprehensive view allows analysts to see and understand everything happening in both the North-South and East-West traffic corridors and at the edges of a network.
Beyond visibility, the Triad also supports detection, investigation and automation. By combining rules and signature-based detections from SIEM and EDR products with real-time behavioral detections powered by machine learning from NDR solutions, analysts can rapidly detect anomalous behaviors and threats at endpoints and in internal traffic. Analysts can then investigate threats and which protocols have been used in an attack with confidence thanks to a full range of information and context supplied by wire data, logs, and agents.
The combined pillars of the Triad can also conduct or support automated or augmented investigation and response, helping relieve the stress felt by overworked and understaffed security teams.
It’s not only security that benefits. IT operations teams using the same network data can identify if there is a performance issue or if it is a security problem, reducing spend, complexity, friction and tool sprawl.
This new security paradigm will become a strategic imperative for enterprises. As more organizations adopt a cloud-first strategy to scale their businesses and increase their agility, they also expand the attack surface and increase exposure to new threats. The introduction of traffic mirroring capabilities for AWS and Azure means that organizations can incorporate this data into their network monitoring analysis and ease the urgent challenges faced by modern enterprise security teams for a more secure future.
Mike Campfield, vice president of global security programs at ExtraHop, authored this article. The views and opinions expressed in this article are those of the author and do not necessarily reflect those of CDOTrends. Photo credit: iStockphoto/FactoryTh









